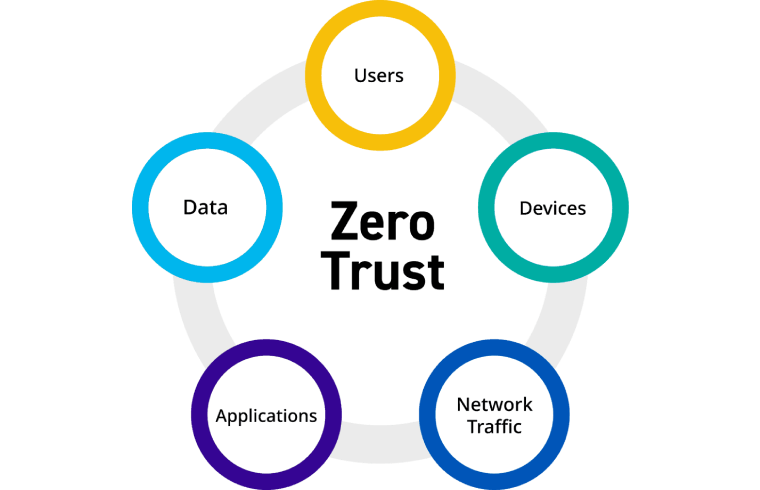
Zero Trust Security: Unlocking Security Benefits While Navigating Common Roadblocks in Your Business
Implementing Zero Trust in a business can bring several benefits, including improved security posture, enhanced data protection, and better overall resilience. However, there are also common roadblocks to watch out for during implementation. Here are the benefits and roadblocks associated with implementing Zero Trust: Benefits of implementing Zero Trust in your business: Increased security: Zero Trust emphasizes continuous verification and strict access controls, reducing the risk of unauthorized access and data breaches. It enables organizations to adopt a proactive security approach by assuming that no user or device can be trusted by default. Better data protection: With Zero Trust, access to sensitive data is strictly controlled and granted on a need-to-know basis. This helps prevent data leakage and unauthorized data access, minimizing the impact of security incidents. Enhanced visibility and control: Zero Trust architectures provide better visibility into network traffic, user behavior, and access patterns. This increased visibility enables organizations to detect anomalies, identify potential threats, and respond swiftly to security incidents. Improved compliance: Zero Trust aligns with many regulatory frameworks and can assist in meeting compliance requirements. By implementing strict access controls, organizations can ensure that only authorized individuals can access sensitive data, reducing the risk of non-compliance. Simplified security management: Zero Trust frameworks often involve consolidating security controls and policies, leading to a more centralized and streamlined security management approach. This can make it easier to enforce security policies and respond to emerging threats. Common roadblocks to watch out for when implementing Zero Trust: Legacy systems and infrastructure: Organizations with older systems and legacy infrastructure may face challenges when implementing Zero Trust. These systems might lack the necessary security features and may require significant updates or replacements to align with the Zero Trust principles. Complexity and implementation effort: Implementing Zero Trust can be a complex undertaking, especially in large organizations with diverse IT environments. It requires a thorough understanding of existing network architectures, access controls, and user behavior patterns. The implementation process might involve significant planning, coordination, and resource allocation. User experience and productivity: Zero Trust implementations can introduce additional authentication steps and access controls, potentially impacting user experience and productivity. It’s important to strike a balance between security and usability to ensure that employees can perform their tasks efficiently without unnecessary hurdles. Cultural and organizational challenges: Adopting a Zero Trust mindset may require a cultural shift within the organization. It might involve changing long-standing security practices and challenging traditional notions of trust. Overcoming resistance to change and fostering a security-conscious culture can be a roadblock that needs to be addressed. Vendor and solution compatibility: Zero Trust often requires integrating multiple security solutions and technologies. Compatibility issues between different vendors’ products or potential gaps in coverage can pose challenges during implementation. Ensuring interoperability and selecting the right mix of solutions is crucial. It’s important to note that while Zero Trust offers significant security advantages, it should be implemented as part of a comprehensive security strategy that includes other essential measures such as regular security assessments, employee training, and incident response planning.